74-MSR係列路由器用L2TP+IPsec+PPPoE實現一總部、多分支式通信配置舉例
本章節下載: 74-MSR係列路由器用L2TP+IPsec+PPPoE實現一總部、多分支式通信配置舉例 (168.33 KB)
MSR係列路由器用L2TP+IPsec+PPPoE實現總部和多分支通信配置舉例
|
Copyright © 2014杭州華三通信技術有限公司 版權所有,保留一切權利。 非經本公司書麵許可,任何單位和個人不得擅自摘抄、複製本文檔內容的部分或全部, 並不得以任何形式傳播。本文檔中的信息可能變動,恕不另行通知。 |
|
目 錄
本文檔介紹MSR係列路由器用L2TP+IPsec+PPPoE實現總部與多分支通信的典型配置舉例。
本文檔不嚴格與具體軟、硬件版本對應,如果使用過程中與產品實際情況有差異,請參考相關產品手冊,或以設備實際情況為準。
本文檔中的配置均是在實驗室環境下進行的配置和驗證,配置前設備的所有參數均采用出廠時的缺省配置。如果您已經對設備進行了配置,為了保證配置效果,請確認現有配置和以下舉例中的配置不衝突。
本文檔假設您已了解L2TP、IPsec和PPPoE特性。
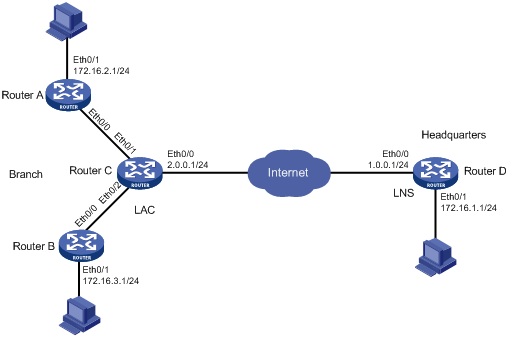
如圖1所示,Router A和Router B是某企業分支網關,Router C為L2TP的LAC,Router D為L2TP的LNS,要求:分支通過PPPoE撥上LAC,並觸發LAC和LNS建立L2TP隧道,實現分支和總部的內網可以互訪。
圖1 MSR係列路由器用L2TP+IPsec+PPPoE實現一總部、多分支式通信配置組網圖
當撥號成功以後,總部網關LNS會給分支網關client分配一個IP地址,總部LNS隻會有分支網關的路由,而不會有分支內網的路由,要實現總部內網和分支內網間的通信要在總部配置一條目的地址為分支內網的靜態路由,下一條指向分支網關,但是分支網關的IP地址是總部LNS這邊的地址池裏麵動態分配的,所以下一條無法定義為具體的IP地址,隻能定義為虛模板。不過這是一總部多分支的組網,所有的L2TP連接都是用的同一虛模板,所以無法滿足用同一個下一跳地址實現和多個分支的通信。在這種情況下隻能在L2TP上複用IPsec來實現路由功能,在LNS的虛接口virtual-template上下發IPsec策略,不同目的地址的數據流會觸發不同的ACL來和不同的IPsec對等體通信,這樣就可以實現一對多的精確路由了。
本舉例是在Release 2317版本上進行配置和驗證的。
· 配置client的時候,要配置一條默認路由,下一跳指向LNS虛模板的地址。
· 配置LNS的安全策略的時候,使用模板,不用配置ACL。
· 分別在分支網關的撥號口和總部網關(LNS)的虛模板接口上下發安全策略。
# 配置接口Ethernet0/1的IP地址。
<RouterA> system-view
[RouterA] interface ethernet 0/1
[RouterA-Ethernet0/1] ip address 172.16.2.1 255.255.255.0
[RouterA-Ethernet0/1] quit
# 配置撥號接口Dialer0,地址協商獲得。
[RouterA] dialer-rule 1 ip permit
[RouterA] interface dialer 0
[RouterA-Dialer0] link-protocol ppp
[RouterA-Dialer0] ppp chap user client1@lac
[RouterA-Dialer0] ppp chap password simple 123
[RouterA-Dialer0] ip address ppp-negotiate
[RouterA-Dialer0] dialer user pppoe
[RouterA-Dialer0] dialer-group 1
[RouterA-Dialer0] dialer bundle 1
[RouterA-Dialer0] quit
# 在接口Ethernet0/0上配置PPPOE會話。
[RouterA] interface ethernet 0/0
[RouterA-Ethernet0/0] pppoe-client dial-bundle-number 1
[RouterA-Ethernet0/0] quit
# 配置默認路由指向Router D。
[RouterA] ip route-static 0.0.0.0 0.0.0.0 100.0.0.1
# 創建ACL,定義觸發IPsec的數據流。
[RouterA] acl number 3000
[RouterA-acl-adv-3000] rule 0 permit ip source 172.16.2.0 0.0.0.255
[RouterA-acl-adv-3000] quit
# 配置IKE對等體。
[RouterA] ike peer peer
[RouterA-ike-peer-peer] exchange-mode aggressive
[RouterA-ike-peer-peer] pre-shared-key 123
[RouterA-ike-peer-peer] id-type name
[RouterA-ike-peer-peer] remote-name center
[RouterA-ike-peer-peer] remote-address 100.0.0.1
[RouterA-ike-peer-peer] quit
# 采用安全提議的缺省配置。
[RouterA] ipsec proposal def
# 配置ESP協議采用md5認證算法。
[RouterA-ipsec-transform-set-def] esp authentication-algorithm md5
[RouterA-ipsec-transform-set-def] quit
# 創建IPsec安全策略policy,其協商方式為isakmp。
[RouterA] ipsec policy policy 1 isakmp
[RouterA-ipsec-policy-isakmp-policy-1] security acl 3000
[RouterA-ipsec-policy-isakmp-policy-1] ike-peer peer
[RouterA-ipsec-policy-isakmp-policy-1] proposal def
[RouterA-ipsec-policy-isakmp-policy-1] quit
# 在撥號接口下應用安全策略。
[RouterA] interface dialer 0
[RouterA-Dialer0] ipsec policy policy
[RouterA-Dialer0] quit
# 配置接口Ethernet0/1的IP地址。
<RouterB> system-view
[RouterB] interface ethernet 0/1
[RouterB-Ethernet0/1] ip address 172.16.3.1 255.255.255.0
[RouterB-Ethernet0/1] quit
# 配置撥號接口Dialer0,地址協商獲得。
[RouterB] interface dialer 0
[RouterB-Dialer0] link-protocol ppp
[RouterB-Dialer0] ppp chap user client2@lac
[RouterB-Dialer0] ppp chap password simple 123
[RouterB-Dialer0] ip address ppp-negotiate
[RouterB-Dialer0] dialer user pppoe
[RouterB-Dialer0] dialer-group 1
[RouterB-Dialer0] dialer bundle 1
[RouterB-Dialer0] quit
# 在接口Ethernet0/0上配置PPPoE會話。
[RouterB] interface ethernet 0/0
[RouterB-Ethernet0/0] pppoe-client dial-bundle-number 1
[RouterB-Ethernet0/0] quit
# 配置默認路由指向Router D。
[RouterB] ip route-static 0.0.0.0 0.0.0.0 100.0.0.1
# 創建ACL,定義觸發IPsec的數據流。
[RouterB] acl number 3000
[RouterB-acl-adv-3000] rule 0 permit ip source 172.16.3.0 0.0.0.255
[RouterB-acl-adv-3000] quit
# 配置IKE對等體。
[RouterB] ike peer peer
[RouterB-ike-peer-peer] exchange-mode aggressive
[RouterB-ike-peer-peer] pre-shared-key 123
[RouterB-ike-peer-peer] id-type name
[RouterB-ike-peer-peer] remote-name center
[RouterB-ike-peer-peer] remote-address 100.0.0.1
[RouterB-ike-peer-peer] quit
# 采用安全提議的缺省配置。
[RouterB] ipsec proposal def
# 配置ESP協議采用md5認證算法。
[RouterB-ipsec-transform-set-def] esp authentication-algorithm md5
[RouterB-ipsec-transform-set-def] quit
# 創建IPsec安全策略policy,其協商方式為isakmp。
[RouterB] ipsec policy policy 1 isakmp
[RouterB-ipsec-policy-isakmp-policy-1] security acl 3000
[RouterB-ipsec-policy-isakmp-policy-1] ike-peer peer
[RouterB-ipsec-policy-isakmp-policy-1] proposal def
[RouterB-ipsec-policy-isakmp-policy-1] quit
# 在撥號接口下應用安全策略。
[RouterB] interface dialer 0
[RouterB-Dialer0] ipsec policy policy
[RouterB-Dialer0] quit
# 啟用L2TP服務。
<RouterC> system-view
[RouterC] l2tp enable
# 采用ISP域的缺省配置。
[RouterC] domain lac
# 設置一個L2TP組,不啟用隧道驗證。
[RouterC] l2tp-group 1
[RouterC-l2tp1] undo tunnel authentication
# 指定LNS的地址及發起L2TP隧道連接的域名。
[RouterC-l2tp1] start l2tp ip 1.0.0.1 domain lac
[RouterC-l2tp1] quit
# 創建本地用戶,配置用戶名、密碼及服務類型。
[RouterC] local-user client1
[RouterC-luser-client1] password simple 123
[RouterC-luser-client1] service-type ppp
[RouterC-luser-client1] quit
[RouterC] local-user client2
[RouterC-luser-client2] password simple 123
[RouterC-luser-client2] service-type ppp
[RouterC-luser-client2] quit
# 配置接口Ethernet0/0的IP地址。
[RouterC] interface ethernet 0/0
[RouterC-Ethernet0/0] ip address 2.0.0.1 255.255.255.0
[RouterC-Ethernet0/0] quit
# 配置虛擬模板接口Virtual-Template0。
[RouterC] interface Virtual-Template0
[RouterC-Virtual-Template0] ppp authentication-mode chap domain lac
[RouterC-Virtual-Template0] quit
# 在接口下將PPPoE服務器與Virtual-Template0綁定。
[RouterC] interface ethernet 0/1
[RouterC-Ethernet0/1] pppoe-server bind virtual-template 0
[RouterC-Ethernet0/1] quit
# 配置接口Ethernet0/0的IP地址。
<RouterD> system-view
[RouterD] interface ethernet 0/0
[RouterD-Ethernet0/0] ip address 1.0.0.1 255.255.255.0
[RouterD-Ethernet0/0] quit
# 配置接口Ethernet0/1的IP地址。
[RouterD] interface ethernet 0/1
[RouterC-Ethernet0/1] ip address 172.16.1.1 255.255.255.0
[RouterC-Ethernet0/1] quit
# 啟用L2TP服務。
[RouterD] l2tp enable
# 采用ISP域的缺省配置。
[RouterD] domain lac
#在域內配置IP地址池,用於分配給client。
[RouterD-isp-lac] ip pool 1 100.0.0.2 100.0.0.255
[RouterD-isp-lac] quit
# 設置一個L2TP組,不啟用隧道驗證。
[RouterD] l2tp-group 1
[RouterD-l2tp1] undo tunnel authentication
# 指定接收呼叫的虛擬模板接口。
[RouterD-l2tp1] allow l2tp Virtual-Template 0
[RouterD-l2tp1] quit
# 配置虛擬模板接口Virtual-Template0。
[RouterD] interface Virtual-Template0
[RouterD-Virtual-Template0] ppp authentication-mode chap domain lac
# 指定對端地址為地址池中的地址。
[RouterD-Virtual-Template0] remote address pool 1
[RouterD-Virtual-Template0] ip address 100.0.0.1 255.255.255.0
[RouterD-Virtual-Template0] quit
# 設置用戶名、密碼及服務類型。
[RouterD] local-user client1
[RouterD-luser-client1] password simple 123
[RouterD-luser-client1] service-type ppp
[RouterD-luser-client1] quit
[RouterD] local-user client2
[RouterD-luser-client2] password simple 123
[RouterD-luser-client2] service-type ppp
[RouterD-luser-client2] quit
# 配置一條默認路由來實現和分支內網的互通。
[RouterD] ip route-static 0.0.0.0 0.0.0.0 Virtual-Template0
# 配置IKE對等體。
[RouterD] ike peer peer
[RouterD-ike-peer-peer] exchange-mode aggressive
[RouterD-ike-peer-peer] pre-shared-key 123
[RouterD-ike-peer-peer] id-type name
[RouterD-ike-peer-peer] remote-name client
[RouterD-ike-peer-peer] quit
# 采用安全提議的缺省配置。
[RouterD] ipsec proposal def
# 配置ESP協議采用md5認證算法。
[RouterD-ipsec-transform-set-def] esp authentication-algorithm md5
[RouterD-ipsec-transform-set-def] quit
# 配置IPsec安全策略模板。
[RouterD] ipsec policy-template test 1
[RouterD-ipsec-policy-template-test-1] ike-peer peer
[RouterD-ipsec-policy-template-test-1] proposal def
[RouterD-ipsec-policy-template-test-1] quit
# 引用IPsec安全策略模板創建一條IPsec安全策略。
[RouterD] ipsec policy policy 1 isakmp template test
# 在虛擬模板接口下應用安全策略。
[RouterD] interface Virtual-Template0
[RouterD-Virtual-Template0] ipsec policy policy
[RouterD-Virtual-Template0] quit
# 可以通過以下顯示信息查看pppoe-client的撥號情況。以Router A為例:
<RouterA> display pppoe-client session packet
PPPoE Client Session:
ID: 1 Interface: Eth0/0
InPackets: 125 OutPackets: 124
InBytes: 1300 OutBytes: 1287
InDrops: 0 OutDrops: 0
# 可以通過以下顯示信息查看LAC端的pppoe-server的撥號情況。
<RouterC> display pppoe-server session packet
Total PPPoE Session(s): 1
SID Intf InP InO InD OutP OutO OutD
1 Eth0/1 176 1807 0 177 1820 0
# 可以通過以下顯示查看LAC端的L2TP會話信息。
<RouterC> display l2tp session
Total session = 1
LocalSID RemoteSID LocalTID
4163 27245 1
<RouterC> display l2tp tunnel
Total tunnel = 1
LocalTID RemoteTID RemoteAddress Port Sessions RemoteName
1 1 1.0.0.1 1701 1 LAC
# 可以通過以下顯示查看LNS端的L2TP會話信息。
<RouterD> display l2tp session
Total session = 1
LocalSID RemoteSID LocalTID
27245 4163 1
<RouterD> display l2tp tunnel
Total tunnel = 1
LocalTID RemoteTID RemoteAddress Port Sessions RemoteName
1 1 1.0.0.2 1701 1 PE1
# 可以通過如下信息看到LNS側可以ping通分支內網。
<RouterD> ping 172.16.2.1
PING 172.16.2.1: 56 data bytes, press CTRL_C to break
Reply from 172.16.2.1: bytes=56 Sequence=0 ttl=255 time=5 ms
Reply from 172.16.2.1: bytes=56 Sequence=1 ttl=255 time=4 ms
Reply from 172.16.2.1: bytes=56 Sequence=2 ttl=255 time=4 ms
Reply from 172.16.2.1: bytes=56 Sequence=3 ttl=255 time=5 ms
Reply from 172.16.2.1: bytes=56 Sequence=4 ttl=255 time=5 ms
--- 172.16.2.1 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 4/4/5 ms
# 可以在Router A、Router B和Router D上通過display ike sa和display ipsec sa查看IPsec建立情況。
· Router A:
#
acl number 3000
rule 0 permit ip source 172.16.2.0 0.0.0.255
#
ike peer peer
exchange-mode aggressive
pre-shared-key cipher $c$3$ABcQkUeBtve6rmSB0B0ej62294PnNg==
id-type name
remote-name center
remote-address 100.0.0.1
#
ipsec transform-set def
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy policy 1 isakmp
security acl 3000
ike-peer peer
transform-set def
#
interface Dialer0
link-protocol ppp
ppp chap user client1@lac
ppp chap password cipher $c$3$oD09I72nb4O+rIS4MUZeDWnHcnOVrRBZ
ip address ppp-negotiate
dialer user pppoe
dialer-group 1
dialer bundle 1
ipsec policy policy
#
interface Ethernet0/1
port link-mode route
ip address 172.16.2.1 255.255.255.0
#
interface Ethernet0/0
port link-mode route
pppoe-client dial-bundle-number 1
#
ip route-static 0.0.0.0 0.0.0.0 100.0.0.1
#
dialer-rule 1 ip permit
#
· Router B:
#
acl number 3000
rule 0 permit ip source 172.16.3.0 0.0.0.255
#
ike peer peer
exchange-mode aggressive
pre-shared-key cipher $c$3$JVGo5rF3xFKO593n6VAFZgE1W7/8Lg==
id-type name
remote-name center
remote-address 100.0.0.1
#
ipsec transform-set def
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy policy 1 isakmp
security acl 3000
ike-peer peer
transform-set def
#
interface Dialer0
link-protocol ppp
ppp chap user client2@lac
ppp chap password cipher $c$3$Zs7w3agJP+iRRBOJicxAdT3AAb4yWLbq
ip address ppp-negotiate
dialer user pppoe
dialer-group 1
dialer bundle 1
ipsec policy policy
#
interface Ethernet0/1
port link-mode route
ip address 172.16.3.1 255.255.255.0
#
interface Ethernet0/0
port link-mode route
pppoe-client dial-bundle-number 1
#
ip route-static 0.0.0.0 0.0.0.0 100.0.0.1
#
dialer-rule 1 ip permit
#
· Router C:
#
l2tp enable
#
domain lac
access-limit disable
state active
idle-cut disable
self-service-url disable
#
local-user client1
password cipher $c$3$8jQGCiqZMOmOQRpUmF/t+gqLoAsQ4Q==
service-type ppp
local-user client2
password cipher $c$3$Flsg/8txuG+/nqXjFIj0OwZzgbw6gg==
service-type ppp
#
l2tp-group 1
undo tunnel authentication
start l2tp ip 1.0.0.1 domain lac
#
interface Ethernet0/0
port link-mode route
ip address 2.0.0.1 255.255.255.0
#
interface Ethernet0/1
port link-mode route
pppoe-server bind Virtual-Template 0
#
interface Virtual-Template0
ppp authentication-mode chap domain lac
#
· Router D:
#
l2tp enable
#
domain lac
access-limit disable
state active
idle-cut disable
self-service-url disable
ip pool 1 100.0.0.2 100.0.0.255
#
ike peer peer
exchange-mode aggressive
pre-shared-key cipher $c$3$f188ftJE8sP8Lu4BXu+DJHn5r4chOw==
id-type name
remote-name client
#
ipsec transform-set def
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy-template test 1
ike-peer peer
transform-set def
#
ipsec policy policy 1 isakmp template test
#
local-user client1
password cipher $c$3$y+FUsYxFVXcTi6eKsHzJZvkdlAdImg==
service-type ppp
local-user client2
password cipher $c$3$JEThVTG4MBHbr18/Wvx3/cC5/6ipCw==
service-type ppp
#
l2tp-group 1
undo tunnel authentication
allow l2tp virtual-template 0
#
interface Ethernet0/0
port link-mode route
ip address 1.0.0.1 255.255.255.0
#
interface Virtual-Template0
ppp authentication-mode chap domain lac
remote address pool 1
ip address 100.0.0.1 255.255.255.0
ipsec policy policy
#
ip route-static 0.0.0.0 0.0.0.0 Virtual-Template0
#
· H3C MSR 係列路由器 命令參考(V5)-R2311
· H3C MSR 係列路由器 配置指導(V5)-R2311
不同款型規格的資料略有差異, 詳細信息請向具體銷售和400谘詢。H3C保留在沒有任何通知或提示的情況下對資料內容進行修改的權利!
