11-MSR係列路由器GRE over IPsec with OSPF典型配置舉例
本章節下載: 11-MSR係列路由器GRE over IPsec with OSPF典型配置舉例 (145.55 KB)
MSR係列路由器GRE over IPsec with OSPF典型配置舉例
|
Copyright © 2014杭州華三通信技術有限公司 版權所有,保留一切權利。 非經本公司書麵許可,任何單位和個人不得擅自摘抄、複製本文檔內容的部分或全部, 並不得以任何形式傳播。本文檔中的信息可能變動,恕不另行通知。 |
|
目 錄
本文檔介紹GRE over IPsec with OSPF的典型配置舉例。
本文檔不嚴格與具體軟、硬件版本對應,如果使用過程中與產品實際情況有差異,請參考相關產品手冊,或以設備實際情況為準。
本文檔中的配置均是在實驗室環境下進行的配置和驗證,配置前設備的所有參數均采用出廠時的缺省配置。如果您已經對設備進行了配置,為了保證配置效果,請確認現有配置和以下舉例中的配置不衝突。
本文檔假設您已了解IPsec、GRE和OSPF特性。
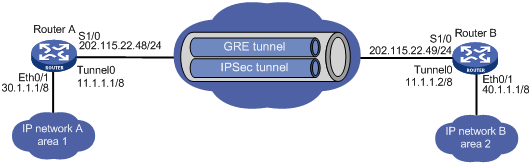
如圖1所示,Router A和Router B是某公司位於不同地點的兩個網絡的網關,要求:
· 建立GRE隧道使內網之間可以互通。
· 在GRE隧道上運行OSPF,傳遞內網路由。
· 建立IPsec隧道,對OSPF的路由信息進行加密,使它安全的穿越外部網絡,而不會泄漏內部網絡的路由。
圖1 GRE over IPsec with OSPF配置組網圖
· 將GRE隧道與OSPF結合使用,可以通過GRE來傳遞OSPF路由,從而使企業私網之間可以互通。
· 將IPsec與GRE結合使用,可以對通過GRE隧道的路由即企業私網間的通信進行保護。
· 將ACL中源、目的IP地址與建立GRE隧道的源、目的IP地址配置相同,可以對整個GRE隧道進行保護。
本舉例是在Release 2207版本上進行配置和驗證的。
不能將建立GRE隧道連接的接口加入到OSPF,否則連接會失效。
# 配置接口Ethernet0/1的IP地址。
<RouterA> system-view
[RouterA] interface ethernet 0/1
[RouterA-Ethernet0/1] ip address 30.1.1.1 255.0.0.0
[RouterA-Ethernet0/1] quit
# 配置接口serial 1/0的IP地址。
[RouterA] interface serial 1/0
[RouterA-Serial1/0] link-protocol ppp
[RouterA-Serial1/0 ]ip address 202.115.22.48 255.255.255.0
[RouterA-Serial1/0] quit
# 創建ACL3000,定義需要IPsec保護的數據流。
[RouterA] acl number 3000
[RouterA-acl-adv-3000] rule 0 permit ip source 202.115.22.48 0 destination 202.115.22.49 0
[RouterA-acl-adv-3000] quit
# 配置IKE對等體。
[RouterA] ike peer test
[RouterA-ike-peer-test] pre-shared-key 123
[RouterA-ike-peer-test] remote-address 202.115.22.49
[RouterA-ike-peer-test] quit
# 配置IPsec安全提議。
[RouterA] ipsec proposal test
[RouterA-ipsec-proposal-test] esp authentication-algorithm sha1
[RouterA-ipsec-proposal-test] esp encryption-algorithm 3des
[RouterA-ipsec-proposal-test] quit
# 配置IPsec策略
[RouterA] ipsec policy test 1 isakmp
[RouterA-ipsec-policy-isakmp-test-1] security acl 3000
[RouterA-ipsec-policy-isakmp-test-1] ike-peer test
[RouterA-ipsec-policy-isakmp-test-1] proposal test
[RouterA-ipsec-policy-isakmp-test-1] quit
# 在接口serial 1/0上應用IPsec策略。
[RouterA] interface serial 1/0
[RouterA-Serial1/0] ipsec policy test
[RouterA-Serial1/0] quit
# 配置GRE隧道。
[RouterA] interface tunnel 0
[RouterA-Tunnel0] ip address 11.1.1.1 255.0.0.0
[RouterA-Tunnel0] source 202.115.22.48
[RouterA-Tunnel0] destination 202.115.22.49
[RouterA-Tunnel0] gre key 4533
[RouterA-Tunnel0] gre checksum
[RouterA-Tunnel0] quit
# 配置OSPF路由協議。
[RouterA] ospf 1
[RouterA-ospf-1] area 0.0.0.0
[RouterA-ospf-1-area-0.0.0.0] network 11.0.0.0 0.255.255.255
[RouterA-ospf-1-area-0.0.0.0] area 0.0.0.1
[RouterA-ospf-1-area-0.0.0.1] network 30.0.0.0 0.255.255.255
[RouterA-ospf-1-area-0.0.0.1] quit
# 配置接口Ethernet0/1的IP地址。
<RouterB> system-view
[RouterB] interface ethernet 0/1
[RouterB-Ethernet0/1] ip address 40.1.1.1 255.0.0.0
[RouterB-Ethernet0/1] quit
# 配置接口serial 1/0的IP地址。
[RouterB] interface serial 1/0
[RouterB-Serial1/0] link-protocol ppp
[RouterB-Serial1/0] ip address 202.115.22.49 255.255.255.0
[RouterB-Serial1/0] quit
# 創建ACL3000,定義需要IPsec保護的數據流。
[RouterB] acl number 3000
[RouterB-acl-adv-3000] rule 0 permit ip source 202.115.22.49 0 destination 202.115.22.48 0
[RouterB-acl-adv-3000] quit
# 配置IKE對等體。
[RouterB]ike peer test
[RouterB-ike-peer-test] pre-shared-key 123
[RouterB-ike-peer-test] remote-address 202.115.22.48
[RouterB-ike-peer-test] quit
# 配置IPsec安全提議。
[RouterB] ipsec proposal test
[RouterB-ipsec-proposal-test] esp authentication-algorithm sha1
[RouterB-ipsec-proposal-test] esp encryption-algorithm 3des
[RouterB-ipsec-proposal-test] quit
# 配置IPsec策略。
[RouterB] ipsec policy test 1 isakmp
[RouterB-ipsec-policy-isakmp-test-1] security acl 3000
[RouterB-ipsec-policy-isakmp-test-1] ike-peer test
[RouterB-ipsec-policy-isakmp-test-1] proposal test
[RouterB-ipsec-policy-isakmp-test-1] quit
# 在接口serial 1/0上應用IPsec策略。
[RouterB] interface serial 1/0
[RouterB-Serial1/0] ipsec policy test
[RouterB-Serial1/0] quit
# 配置GRE隧道。
[RouterB] interface tunnel 0
[RouterB-Tunnel0] ip address 11.1.1.2 255.0.0.0
[RouterB-Tunnel0] source 202.115.22.49
[RouterB-Tunnel0] destination 202.115.22.48
[RouterB-Tunnel0] gre key 4533
[RouterB-Tunnel0] gre checksum
[RouterB-Tunnel0] quit
# 配置OSPF路由協議。
[RouterB] ospf 1
[RouterB-ospf-1] area 0.0.0.0
[RouterB-ospf-1-area-0.0.0.0] network 11.0.0.0 0.255.255.255
[RouterB-ospf-1-area-0.0.0.0] area 0.0.0.2
[RouterB-ospf-1-area-0.0.0.2] network 40.0.0.0 0.255.255.255
[RouterB-ospf-1-area-0.0.0.2] quit
# 配置完成後OSPF通過GRE的tunnel接口向外發送hello報文,由於hello報文經過GRE封裝,匹配了acl規則,因此觸發了ike協商。在OSPF建立鄰居關係的同時,IPsec經過協商後也會建立起IPsec隧道。以Router A為例,使用display ike sa命令可以查看sa建立情況。
<RouterA> display ike sa
total phase-1 SAs: 1
connection-id peer flag phase doi
----------------------------------------------------------------
8 202.115.22.49 RD|ST 1 IPSEC
9 202.115.22.49 RD|ST 2 IPSEC
flag meaning
RD--READY ST--STAYALIVE RL--REPLACED FD--FADING TO--TIMEOUT
# 在係統視圖下使用display ipsec sa命令可以看到ipsec sa的建立情況。
<RouterA> display ipsec sa
===============================
Interface: Serial1/0
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "test"
sequence number: 1
mode: isakmp
-----------------------------
connection id: 1
encapsulation mode: tunnel
perfect forward secrecy:
tunnel:
local address: 202.115.22.48
remote address: 202.115.22.49
flow:
sour addr: 202.115.22.48/255.255.255.255 port: 0 protocol: IP
dest addr: 202.115.22.49/255.255.255.255 port: 0 protocol: IP
[inbound ESP SAs]
spi: 54798862 (0x3442a0e)
proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843197/3390
max received sequence-number: 25
anti-replay check enable: Y
anti-replay window size: 32
udp encapsulation used for nat traversal: N
[outbound ESP SAs]
spi: 2040435079 (0x799e9187)
proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843196/3390
max received sequence-number: 31
udp encapsulation used for nat traversal: N
# 在係統視圖下使用display ipsec tunnel命令可以看到隧道的統計信息。
<RouterA> display ipsec tunnel
total tunnel : 1
------------------------------------------------
connection id: 1
perfect forward secrecy:
SA's SPI:
inbound: 54798862 (0x3442a0e) [ESP]
outbound: 2040435079 (0x799e9187) [ESP]
tunnel:
local address: 202.115.22.48
remote address: 202.115.22.49
flow:
sour addr: 202.115.22.48/255.255.255.255 port: 0 protocol: IP
dest addr: 202.115.22.49/255.255.255.255 port: 0 protocol: IP
current Encrypt-card:
· Router A:
#
acl number 3000
rule 0 permit ip source 202.115.22.48 0 destination 202.115.22.49 0
#
ike peer test
pre-shared-key cipher pTHDptKNjg0=
remote-address 202.115.22.49
#
ipsec proposal test
esp authentication-algorithm sha1
esp encryption-algorithm 3des
#
ipsec policy test 1 isakmp
security acl 3000
ike-peer test
proposal test
#
interface Ethernet0/1
port link-mode route
ip address 30.1.1.1 255.0.0.0
#
interface Serial1/0
link-protocol ppp
ip address 202.115.22.48 255.255.255.0
ipsec policy test
#
interface Tunnel0
ip address 11.1.1.1 255.0.0.0
source 202.115.22.48
destination 202.115.22.49
gre key 4533
gre checksum
#
ospf 1
area 0.0.0.0
network 11.0.0.0 0.255.255.255
area 0.0.0.1
network 30.0.0.0 0.255.255.255
#
· Router B:
#
acl number 3000
rule 0 permit ip source 202.115.22.49 0 destination 202.115.22.48 0
#
ike peer test
pre-shared-key cipher pTHDptKNjg0=
remote-address 202.115.22.48
#
ipsec proposal test
esp authentication-algorithm sha1
esp encryption-algorithm 3des
#
ipsec policy test 1 isakmp
security acl 3000
ike-peer test
proposal test
#
interface Ethernet0/1
port link-mode route
ip address 40.1.1.1 255.0.0.0
#
interface Serial1/0
port link-protocol ppp
ip address 202.115.22.49 255.255.255.0
ipsec policy test
#
interface Tunnel0
ip address 11.1.1.2 255.0.0.0
source 202.115.22.49
destination 202.115.22.48
gre key 4533
gre checksum
#
ospf 1
area 0.0.0.0
network 11.0.0.0 0.255.255.255
area 0.0.0.2
network 40.0.0.0 0.255.255.255
#
· H3C MSR 係列路由器 命令參考(V5)-R2311
· H3C MSR 係列路由器 配置指導(V5)-R2311
不同款型規格的資料略有差異, 詳細信息請向具體銷售和400谘詢。H3C保留在沒有任何通知或提示的情況下對資料內容進行修改的權利!
