有沒有防火牆F1030一個總部對多個分部的ipsec vpn的案例啊
- 0關注
- 0收藏,1513瀏覽
最佳答案

一對一與一對多原理是一樣,參考這個就行。
找自己符合需求的,都是固定IP還是有一端是撥號。固定主模式,不固定野蠻模式。
鏈接://www.yolosolive.com/cn/d_202311/1968517_30005_0.htm#_Toc150941556
如需登陸,賬號yx800 密碼01230123



- 2024-01-08回答
- 評論(0)
- 舉報
-
(0)
暫無評論

您好,請知:
以下是配置案例,請參考:

總部公網地址172.16.0.1,分支無論地址是否固定。兩邊私網地址用loopback地址替代。
配置步驟
地址、安全域及安全策略需自行配置放通
一、總部配置
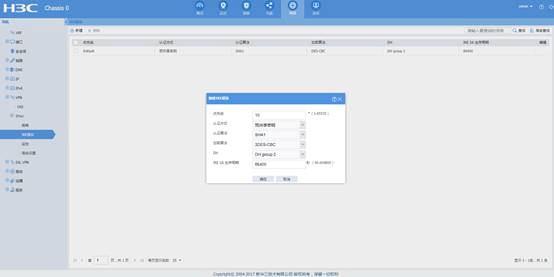
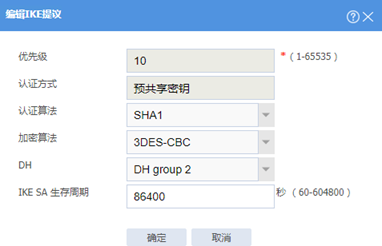
新建ike提議
網絡》VPN》ipsec》IKE提議》新建,選擇相應的認證加密等參數
認證加密等參數相同的ike提議建議隻配置一個,因為參數相同設備隻會去匹配優先級最高的那個ike提議,優先級數值越小越優先。
新建ipsec策略
網絡》VPN》ipsec》策略》新建,新建相應的ipsec策略等參數
配置ipsec策略的名稱,選擇接口及地址,總部設備角色選擇中心節點。選擇中心節點設備會下發模板方式的配置。模板方式的總部不需要配置acl,由分支配置acl來跟總部協商自動出保護的數據流。
IKE策略選擇野蠻模式,IKE提議選擇之前配置的ike,本端ID選擇ipv4地址。
注意:本端ID一定要選擇ipv4地址

Ipsec參數選擇esp認證加密算法,其他保持默認。

二、分支配置
配置ike提議
網絡》VPN》ipsec》IKE提議》新建,選擇相應的認證加密等參數,同總部配置
配置ipsec策略和ike策略
網絡》VPN》ipsec》策略》新建,新建相應的ipsec策略等參數
注意:本端ID留空,對端ID選擇ipv4地址

配置ipsec保護的數據流及ipsec參數

配置關鍵點
總部采用模板方式無法指定分支的FQDN,總部默認下發配置
ike profile zongbu_IPv4_1
keychain zongbu_IPv4_1
exchange-mode aggressive
local-identity address 172.16.0.1
match remote identity address 0.0.0.0 0.0.0.0
match local address GigabitEthernet1/0/0
proposal 10
指定對端地址為全0,所以分支隻能配置身份識別local-identity為地址,又因為大部分采用野蠻模式的分支地址是不固定的,所以分支這裏本端ID隻能留空,默認local-identity為地址。否則兩端因為身份識別方式不一致導致協商不起來。

分支IKE策略--對端ID必須配置ipv4地址,因為分支要主動發起必須知道總部地址,另外如果分支對端ID配置成FQDN的話,下發配置如下。
ike profile fenzhi_IPv4_1
keychain fenzhi_IPv4_1
exchange-mode aggressive
local-identity fqdn fenzhi
match remote identity fqdn zongbu
match local address GigabitEthernet1/0/0
proposal 10
#
ike proposal 10
encryption-algorithm 3des-cbc
dh group2
#
ike keychain fenzhi_IPv4_1
match local address GigabitEthernet1/0/0
pre-shared-key hostname zongbu key cipher $c$3$U4JtiyOgrXVs/aYytzz3IeVQFWDORDQ7
秘鑰會指定為hostname,會報找不到對應的密鑰從而ike都無法建立。
命令行配置如下:
總部配置
<zongbu>dis cu
#
version 7.1.064, Alpha 7164
#
sysname zongbu
#
context Admin id 1
#
telnet server enable
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
ospf 1
area 0.0.0.0
network 172.16.0.0 0.0.0.255
#
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
interface NULL0
#
interface LoopBack0
ip address 1.1.1.1 255.255.255.255
#
interface GigabitEthernet1/0/0
port link-mode route
combo enable copper
ip address 172.16.0.1 255.255.255.0
ipsec apply policy zongbu
#
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
ip address 172.16.2.1 255.255.255.0
#
interface GigabitEthernet1/0/2
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/3
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/4
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/5
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/6
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/7
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/8
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/9
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/10
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/11
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/12
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/13
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/14
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/15
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/16
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/17
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/18
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/19
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/20
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/21
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/22
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/23
port link-mode route
combo enable copper
#
security-zone name Local
#
security-zone name Trust
import interface LoopBack0
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/0
import interface GigabitEthernet1/0/1
#
security-zone name Management
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 4
authentication-mode scheme
user-role network-admin
#
line vty 5 63
user-role network-operator
#
ip route-static 0.0.0.0 0 172.16.0.2
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$UbIhNnPevyKUwfpm$LqR3+yg1IjNct39MkOR0H0iQXLkYB3jMqM4vbAeoXOhbabIIFnjJPEGR00YiYA1Sz4LiY3FmEdru2fOLMb1shQ==
service-type telnet terminal http
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ipsec transform-set zongbu_IPv4_1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm sha1
#
ipsec policy-template zongbu 1
transform-set zongbu_IPv4_1
local-address 172.16.0.1
ike-profile zongbu_IPv4_1
#
ipsec policy zongbu 1 isakmp template zongbu
#
ike profile zongbu_IPv4_1
keychain zongbu_IPv4_1
exchange-mode aggressive
local-identity address 172.16.0.1
match remote identity address 0.0.0.0 0.0.0.0
match local address GigabitEthernet1/0/0
proposal 10
#
ike proposal 10
encryption-algorithm 3des-cbc
dh group2
#
ike keychain zongbu_IPv4_1
match local address GigabitEthernet1/0/0
pre-shared-key address 0.0.0.0 0.0.0.0 key cipher $c$3$nw8o7yIcjPSdFyAURIYIKXSd/sFIJgEN
#
ip http enable
ip https enable
#
security-policy ip
rule 1 name test
action pass
#
return
<zongbu>
<zongbu>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
9 172.16.1.1 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<zongbu>dis ipse
<zongbu>dis ipsec sa
<zongbu>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/0
-------------------------------
-----------------------------
IPsec policy: zongbu
Sequence number: 1
Mode: Template
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 172.16.0.1
remote address: 172.16.1.1
Flow:
sour addr: 1.1.1.1/255.255.255.255 port: 0 protocol: ip
dest addr: 2.2.2.2/255.255.255.255 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1511053843 (0x5a10da13)
Connection ID: 12884901891
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/2576
Max received sequence-number: 5
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 3440085931 (0xcd0b8bab)
Connection ID: 12884901890
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/2576
Max sent sequence-number: 5
UDP encapsulation used for NAT traversal: N
Status: Active
<zongbu>
分支配置
<fenzhi>dis cu
#
version 7.1.064, Alpha 7164
#
sysname fenzhi
#
context Admin id 1
#
telnet server enable
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
ospf 1
area 0.0.0.0
network 172.16.1.0 0.0.0.255
#
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
interface NULL0
#
interface LoopBack0
ip address 2.2.2.2 255.255.255.255
#
interface GigabitEthernet1/0/0
port link-mode route
combo enable copper
ip address 172.16.1.1 255.255.255.0
ipsec apply policy fenzhi
#
interface GigabitEthernet1/0/1
port link-mode route
combo enable copper
ip address 172.16.2.2 255.255.255.0
#
interface GigabitEthernet1/0/2
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/3
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/4
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/5
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/6
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/7
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/8
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/9
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/10
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/11
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/12
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/13
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/14
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/15
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/16
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/17
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/18
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/19
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/20
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/21
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/22
port link-mode route
combo enable copper
#
interface GigabitEthernet1/0/23
port link-mode route
combo enable copper
#
security-zone name Local
#
security-zone name Trust
import interface LoopBack0
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/0
import interface GigabitEthernet1/0/1
#
security-zone name Management
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 4
authentication-mode none
user-role network-admin
#
line vty 5 63
authentication-mode none
user-role network-operator
#
ip route-static 0.0.0.0 0 172.16.1.2
#
acl advanced name IPsec_fenzhi_IPv4_1
rule 1 permit ip source 2.2.2.2 0 destination 1.1.1.1 0
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$UbIhNnPevyKUwfpm$LqR3+yg1IjNct39MkOR0H0iQXLkYB3jMqM4vbAeoXOhbabIIFnjJPEGR00YiYA1Sz4LiY3FmEdru2fOLMb1shQ==
service-type telnet terminal http
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ipsec transform-set fenzhi_IPv4_1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm sha1
#
ipsec policy fenzhi 1 isakmp
transform-set fenzhi_IPv4_1
security acl name IPsec_fenzhi_IPv4_1
remote-address 172.16.0.1
ike-profile fenzhi_IPv4_1
#
ike profile fenzhi_IPv4_1
keychain fenzhi_IPv4_1
exchange-mode aggressive
match remote identity address 172.16.0.1 255.255.255.255
match local address GigabitEthernet1/0/0
proposal 10
#
ike proposal 10
encryption-algorithm 3des-cbc
dh group2
#
ike keychain fenzhi_IPv4_1
match local address GigabitEthernet1/0/0
pre-shared-key address 172.16.0.1 255.255.255.255 key cipher $c$3$0D8k6aHsDClx2d/siPNHdmCMjeDjWHJR
#
ip http enable
ip https enable
#
security-policy ip
rule 1 name test
action pass
#
return
<fenzhi>
<fenzhi>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
37 172.16.0.1 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<fenzhi>dis ipse
<fenzhi>dis ipsec sa
<fenzhi>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/0
-------------------------------
-----------------------------
IPsec policy: fenzhi
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1444
Tunnel:
local address: 172.16.1.1
remote address: 172.16.0.1
Flow:
sour addr: 2.2.2.2/255.255.255.255 port: 0 protocol: ip
dest addr: 1.1.1.1/255.255.255.255 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 3440085931 (0xcd0b8bab)
Connection ID: 12884901891
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/2400
Max received sequence-number: 5
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 1511053843 (0x5a10da13)
Connection ID: 12884901890
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843199/2400
Max sent sequence-number: 5
UDP encapsulation used for NAT traversal: N
Status: Active
- 2024-01-08回答
- 評論(0)
- 舉報
-
(0)
暫無評論
編輯答案


親~登錄後才可以操作哦!
確定你的郵箱還未認證,請認證郵箱或綁定手機後進行當前操作
舉報
×
侵犯我的權益
×
侵犯了我企業的權益
×
- 1. 您舉報的內容是什麼?(請在郵件中列出您舉報的內容和鏈接地址)
- 2. 您是誰?(身份證明材料,可以是身份證或護照等證件)
- 3. 是哪家企業?(營業執照,單位登記證明等證件)
- 4. 您與該企業的關係是?(您是企業法人或被授權人,需提供企業委托授權書)
抄襲了我的內容
×
原文鏈接或出處
誹謗我
×
- 1. 您舉報的內容以及侵犯了您什麼權益?(請在郵件中列出您舉報的內容、鏈接地址,並給出簡短的說明)
- 2. 您是誰?(身份證明材料,可以是身份證或護照等證件)
對根叔社區有害的內容
×
不規範轉載
×
舉報說明




暫無評論