組網及說明
配置需求及實現的效果
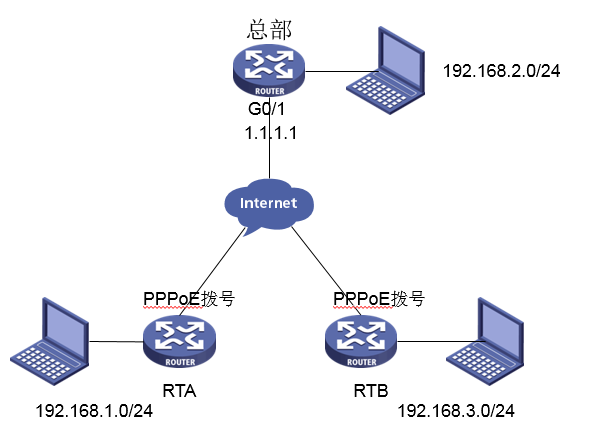
MSR 分支路由器采用PPPoE撥號方式上網,IP地址不固定,MSR 總部路由器外網口G0/1的地址為1.1.1.1(模擬運營商公網固定地址環境)。要實現對分支1所在的內網(192.168.1.0/24)與分支2路由器所在的內網(192.168.3.0/24)之間的數據流進行安全保護,實現兩端內網終端通過與總部建立IPsec VPN 隧道進行互訪。
配置步驟
1. 設置總部路由器IPSEC VPN
#配置一個訪問控製列表3000,定義由總部子網192.168.2.0/24去分支1子網192.168.1.0/24和分支2子網192.168.3.0/24去分支1子網192.168.1.0/24的數據流
<H3C>system-view
[H3C]acl number 3000
[H3C-acl-adv-3000]rule 0 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-adv-3000]rule 1 permit ip source 192.168.3.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-adv-3000]quit
#配置一個訪問控製列表3001,定義由總部子網192.168.2.0/24去分支2子網192.168.1.0/24和分支1子網192.168.3.0/24去分支2子網192.168.1.0/24的數據流
[H3C]acl number 3001
[H3C-acl-adv-3001]rule 0 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
[H3C-acl-adv-3001]rule 1 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
[H3C-acl-adv-3001]quit
#配置公網口NAT要關聯的ACl 3002,作用是把IPSec感興趣流從NAT轉換的數據流deny掉,防止IPSec數據流被NAT優先轉換
[H3C]acl number 3002
[H3C-acl-adv-3002]rule 0 deny ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-adv-3002]rule 1 deny ip source 192.168.3.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-adv-3002]rule 2 deny ip source 192.168.2.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
[H3C-acl-adv-3002]rule 3 deny ip source 192.168.1.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
[H3C-acl-adv-3002]rule 4 permit ip
[H3C-acl-adv-3002]quit
#創建一條IKE提議1,指定IKE提議使用的認證算法為MD5,加密算法為3des-cbc
[H3C]ike proposal 1
[H3C-ike-proposal-1]authentication-algorithm md5
[H3C-ike-proposal-1]encryption-algorithm 3des-cbc
[H3C-ike-proposal-1]quit
#配置本端FQDN名稱為zongbu
[H3C]ike identity fqdn zongbu
#創建並配置IKE keychain,名稱為RTA和RTB
[H3C]ike keychain RTA
#配置與分支之間協商采用的預共享密鑰,(由於分支設備無固定IP,這裏需要采用name的方式),這裏配置分支1的name為RTA,分支2的name為RTB,分支name需要與分支側設置的一致,使用的預共享密鑰為明文123456
[H3C-ike-keychain-RTA]pre-shared-key hostname RTA key simple 123456
[H3C-ike-keychain-RTA]quit
[H3C]ike keychain RTB
[H3C-ike-keychain-RTB]pre-shared-key hostname RTB key simple 123456
[H3C-ike-keychain-RTB]quit
#創建並配置IKE profile,名稱分別為RTA和RTB,引用上麵配置的keychain,配置IKE第一階段的協商模式為野蠻模式,本端身份類型為FQDN且取值為zongbu,指定需要匹配對端身份類型為FQDN且取值RTA和RTB,引用之前配置IKE提議1
[H3C]ike profile RTA
[H3C-ike-profile-RTA]keychain RTA
[H3C-ike-profile-RTA]exchange-mode aggressive
[H3C-ike-profile-RTA]local-identity fqdn zongbu
[H3C-ike-profile-RTA]match remote identity fqdn RTA
[H3C-ike-profile-RTA]proposal 1
[H3C-ike-profile-RTA]quit
[H3C]ike profile RTB
[H3C-ike-profile-RTB]keychain RTB
[H3C-ike-profile-RTB]exchange-mode aggressive
[H3C-ike-profile-RTB]local-identity fqdn zongbu
[H3C-ike-profile-RTB]match remote identity fqdn RTB
[H3C-ike-profile-RTB]proposal 1
[H3C-ike-profile-RTB]quit
#配置IPsec安全提議1,ESP協議采用的加密算法為3des-cbc,認證算法為md5
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1]encapsulation-mode tunnel
[H3C-ipsec-transform-set-1]esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-1]esp authentication-algorithm md5
[H3C-ipsec-transform-set-1]quit
#創建兩個模板名字分別為t1和t2,順序號為1的安全策略模板,引用之前創建的ACL3000和3001,引用之前創建的IKE profile,引用之前的IPSec安全提議1
[H3C]ipsec policy-template t1 1
[H3C-ipsec-policy-template-t1-1]security acl 3000
[H3C-ipsec-policy-template-t1-1]ike-profile RTA
[H3C-ipsec-policy-template-t1-1]transform-set 1
[H3C-ipsec-policy-template-t1-1]quit
[H3C]ipsec policy-template t2 1
[H3C-ipsec-policy-template-t2-1]security acl 3001
[H3C-ipsec-policy-template-t2-1]ike-profile RTB
[H3C-ipsec-policy-template-t2-1]transform-set 1
[H3C-ipsec-policy-template-t2-1]quit
#
[H3C] ipsec policy zongbu 1 isakmp template t1
[H3C] ipsec policy zongbu 2 isakmp template t2
#設置外網口做NAT轉換的時候關聯ACL 3002 (如果之前已經在外網口配置了 nat outbound,需要先undo掉),並將IPSec安全策略v7應用在外網接口
[H3C]interface GigabitEthernet 0/1
[H3C-GigabitEthernet0/1]undo nat outbound
[H3C-GigabitEthernet0/1]nat outbound 3002
[H3C-GigabitEthernet0/1]ipsec apply policy zongbu
[H3C-GigabitEthernet0/1]quit
#保存配置
[H3C]save force
2. 設置分支1路由器IPSEC VPN
#配置一個訪問控製列表,定義由分支1子網192.168.1.0/24去總部子網192.168.2.0/24,分支1子網192.168.1.0/24去分支2子網192.168.3.0/24的數據流
<H3C>system-view
[H3C]acl advanced 3000
[H3C-acl-ipv4-adv-3000]rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
[H3C-acl-ipv4-adv-3000]rule 1 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
[H3C-acl-ipv4-adv-3000]quit
#配置公網口NAT要關聯的ACl 3001,作用是把IPSec感興趣流從NAT轉換的數據流deny掉,防止IPSec數據流被NAT優先轉換
[H3C]acl advanced 3001
[H3C-acl-ipv4-adv-3001]rule 0 deny ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
[H3C-acl-ipv4-adv-3001]rule 1 deny ip source 192.168.1.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
[H3C-acl-ipv4-adv-3001]rule 2 permit ip
[H3C-acl-adv-3001]quit
#創建一條IKE提議1,指定IKE提議使用的認證算法為MD5,加密算法為3des-cbc
[H3C]ike proposal 1
[H3C-ike-proposal-1]authentication-algorithm md5
[H3C-ike-proposal-1]encryption-algorithm 3des-cbc
[H3C-ike-proposal-1]quit
#配置本端FQDN名稱為RTA
[H3C]ike identity fqdn RTA
#創建並配置IKE keychain,名稱為RTA。
[H3C]ike keychain RTA
#配置對端IP地址為1.1.1.1,使用的預共享密鑰為明文123456
[H3C-ike-keychain-RTA]pre-shared-key address 1.1.1.1 key simple 123456
[H3C-ike-keychain-RTA]quit
#創建並配置IKE profile,名稱為RTA,引用上麵配置的keychain RTA,配置IKE第一階段的協商模式為野蠻模式,本端身份類型為FQDN且取值為RTA,指定需要匹配對端身份類型為FQDN且取值zongbu,引用之前配置IKE提議1
[H3C]ike profile RTA
[H3C-ike-profile-RTA]keychain RTA
[H3C-ike-profile-RTA]exchange-mode aggressive
[H3C-ike-profile-RTA]local-identity fqdn RTA
[H3C-ike-profile-RTA]match remote identity fqdn zongbu
[H3C-ike-profile-RTA]proposal 1
[H3C-ike-profile-RTA]quit
#配置IPsec安全提議1,ESP協議采用的加密算法為3des-cbc,認證算法為md5
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1]esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-1]esp authentication-algorithm md5
[H3C-ipsec-transform-set-1]quit
#創建一條IPSec安全策略RTA,協商方式為isakmp。引用之前創建的感興趣數據流ACL3000,指定對端公網ip地址,引用之前創建的IKE profile,引用之前的IPSec安全提議1
[H3C]ipsec policy RTA 1 isakmp
[H3C-ipsec-policy-isakmp-RTA-1]security acl 3000
[H3C-ipsec-policy-isakmp-RTA-1]remote-address 1.1.1.1
[H3C-ipsec-policy-isakmp-RTA-1]ike-profile RTA
[H3C-ipsec-policy-isakmp-RTA-1]transform-set 1
[H3C-ipsec-policy-isakmp-RTA-1]quit
#設置外網口(在本例中假設撥號口為Dialer 10)做NAT轉換的時候關聯ACL 3001 (如果之前已經在外網口配置了 nat outbound,需要先undo掉),並將IPSec安全策略RTA應用在外網接口,
[H3C]interface Dialer 10
[H3C-Dialer10]undo nat outbound
[H3C-Dialer10]nat outbound 3001
[H3C-Dialer10]ipsec apply policy RTA
[H3C-Dialer10]quit
#保存配置
[H3C]save force
3. 設置分支2路由器IPSEC VPN
#配置一個訪問控製列表,定義由分支2子網192.168.3.0/24去總部子網192.168.2.0/24,分支2子網192.168.3.0/24去分支1子網192.168.1.0/24的數據流
<H3C>system-view
[H3C]acl advanced 3000
[H3C-acl-ipv4-adv-3000]rule 0 permit ip source 192.168.3.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
[H3C-acl-ipv4-adv-3000]rule 1 permit ip source 192.168.3.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-ipv4-adv-3000]quit
#配置公網口NAT要關聯的ACl 3001,作用是把IPSec感興趣流從NAT轉換的數據流deny掉,防止IPSec數據流被NAT優先轉換
[H3C]acl advanced 3001
[H3C-acl-ipv4-adv-3001]rule 0 deny ip source 192.168.3.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
[H3C-acl-ipv4-adv-3001]rule 1 deny ip source 192.168.3.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-ipv4-adv-3001]rule 2 permit ip
[H3C-acl-adv-3001]quit
#創建一條IKE提議1,指定IKE提議使用的認證算法為MD5,加密算法為3des-cbc
[H3C]ike proposal 1
[H3C-ike-proposal-1]authentication-algorithm md5
[H3C-ike-proposal-1]encryption-algorithm 3des-cbc
[H3C-ike-proposal-1]quit
#配置本端FQDN名稱為RTB
[H3C]ike identity fqdn RTB
#創建並配置IKE keychain,名稱為RTB。
[H3C]ike keychain RTB
#配置對端IP地址為1.1.1.1,使用的預共享密鑰為明文123456
[H3C-ike-keychain-RTB]pre-shared-key address 1.1.1.1 key simple 123456
[H3C-ike-keychain-RTB]quit
#創建並配置IKE profile,名稱為RTA,引用上麵配置的keychain RTB,配置IKE第一階段的協商模式為野蠻模式,本端身份類型為FQDN且取值為RTB,指定需要匹配對端身份類型為FQDN且取值zongbu,引用之前配置IKE提議1
[H3C]ike profile RTB
[H3C-ike-profile-RTB]keychain RTB
[H3C-ike-profile-RTB]exchange-mode aggressive
[H3C-ike-profile-RTB]local-identity fqdn RTB
[H3C-ike-profile-RTB]match remote identity fqdn zongbu
[H3C-ike-profile-RTB]proposal 1
[H3C-ike-profile-RTB]quit
#配置IPsec安全提議1,ESP協議采用的加密算法為3des-cbc,認證算法為md5
[H3C]ipsec transform-set 1
[H3C-ipsec-transform-set-1]esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-1]esp authentication-algorithm md5
[H3C-ipsec-transform-set-1]quit
#創建一條IPSec安全策略RTB,協商方式為isakmp。引用之前創建的感興趣數據流ACL3000,指定對端公網ip地址,引用之前創建的IKE profile,引用之前的IPSec安全提議1
[H3C]ipsec policy RTB 1 isakmp
[H3C-ipsec-policy-isakmp-RTB-1]security acl 3000
[H3C-ipsec-policy-isakmp-RTB-1]ike-profile RTB
[H3C-ipsec-policy-isakmp-RTB-1]remote-address 1.1.1.1
[H3C-ipsec-policy-isakmp-RTB-1]transform-set 1
[H3C-ipsec-policy-isakmp-RTB-1]quit
#設置外網口(在本例中假設撥號口為Dialer 10)做NAT轉換的時候關聯ACL 3001 (如果之前已經在外網口配置了 nat outbound,需要先undo掉),並將IPSec安全策略RTA應用在外網接口,
[H3C]interface Dialer 10
[H3C-Dialer10]undo nat outbound
[H3C-Dialer10]nat outbound 3001
[H3C-Dialer10]ipsec apply policy RTB
[H3C-Dialer10]quit
#保存配置
[H3C]save force
該案例暫時沒有網友評論
編輯評論
✖
案例意見反饋


親~登錄後才可以操作哦!
確定你的郵箱還未認證,請認證郵箱或綁定手機後進行當前操作
